Promotron vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
Promotron
Promotron revolutionizes the promotional industry with automated sales, collaboration, and cloud-driven e-commerce.
Last updated: February 28, 2026
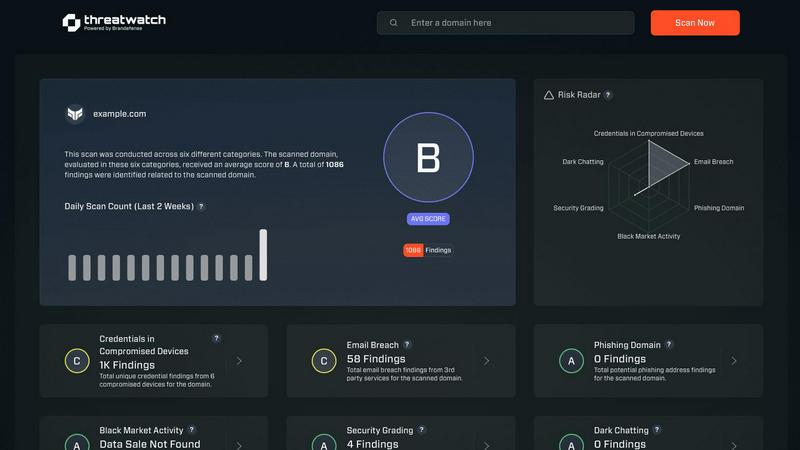
Threat Watch
Take command of your digital safety with an instant, comprehensive cybersecurity health scan.
Last updated: March 1, 2026
Visual Comparison
Promotron
Threat Watch
Feature Comparison
Promotron
Unique Web2Print Technology
Promotron's innovative Web2Print technology allows users to generate print-ready data and conduct proofreading in just 60 seconds. This feature drastically reduces the time spent on print preparations, enabling quicker turnaround times for promotional products and textiles.
Automated Quoting System
With Promotron's automated quoting feature, users can create detailed quotes, including print prices and virtual samples, in under a minute. This capability enhances productivity, allowing businesses to respond swiftly to customer inquiries and maintain a competitive edge.
Advanced Online Print Calculator
The platform includes an advanced online print calculator specifically designed for promotional products and textiles. This tool helps users estimate costs accurately, ensuring transparency and efficiency in the pricing process, while also empowering customers to make informed purchasing decisions.
First-Class E-commerce Solutions
Promotron offers a state-of-the-art webshop for online sales of promotional goods and textiles, fully integrated with printing capabilities. This allows businesses to sell custom-made products effortlessly and provides a seamless shopping experience for customers, enhancing engagement and satisfaction.
Threat Watch
Comprehensive Digital Footprint Analysis
Threat Watch goes beyond surface-level scanning to deliver a deep, continuous analysis of your entire digital presence. It automatically discovers and inventories all internal and external assets, including cloud instances, domains, and network devices, while simultaneously hunting for associated vulnerabilities. This 360-degree visibility ensures no blind spot is left unmonitored, giving you the complete picture needed for true security confidence.
Dark Web & Breach Intelligence Monitoring
Proactively defend against threats that originate in the shadows. Threat Watch constantly monitors dark web forums, paste sites, and private channels for mentions of your company's data, such as stolen credentials, intellectual property, or confidential plans. This early-warning system alerts you to breaches involving your employees or systems long before they can be weaponized, allowing for preemptive action.
Real-Time Compromised Credential Alerts
One of the most common attack vectors is through reused or leaked passwords. Threat Watch integrates with vast databases of known breaches to instantly alert you if employee email addresses and credentials appear in compromised data sets. This allows your security team to enforce immediate password resets and multi-factor authentication, shutting down account takeover attempts before they begin.
Actionable Risk Prioritization Dashboard
Information overload is paralyzing. Threat Watch cuts through the noise by synthesizing millions of data points into a clear, prioritized risk score and actionable insights. The intuitive dashboard categorizes risks by severity and potential business impact, telling you exactly what to fix first. This transforms raw data into a strategic roadmap, enabling efficient resource allocation and faster risk reduction.
Use Cases
Promotron
For Distributors and Resellers
Distributors can leverage Promotron to provide powerful e-commerce solutions that elevate the shopping experience for their customers. By accessing a vast array of products from multiple EU importers, they can easily expand their offerings and attract new clients while retaining existing ones.
For Importers and Wholesalers
Importers and wholesalers can utilize Promotron to enhance their B2B networks, making it easier for distributors to access their products. With unique presentation tools, including 3D product views, they can effectively showcase bestsellers and drive sales through modern webshops.
For Manufacturers and Producers
Manufacturers can harness the unique tools offered by Promotron to effectively present and sell their products online. By connecting with new distributors across the EU, they can expand their market reach while supporting B2B partners with innovative e-commerce solutions.
For Printing Houses
Printing houses can transform their business model by integrating promotional products into their offerings. With Promotron, they can set up a webshop at minimal costs, enabling them to sell thousands of products online while also speeding up the graphic proof process for customer satisfaction.
Threat Watch
Proactive External Attack Surface Management
Security teams use Threat Watch to continuously discover and assess all internet-facing assets owned by their organization. By identifying unknown or forgotten servers, misconfigured cloud storage, and vulnerable web applications, they can eliminate easy entry points for attackers before a breach occurs, dramatically hardening their external defenses.
Rapid Incident Response & Investigation
When a security alert fires, every second counts. Investigators leverage Threat Watch to instantly cross-reference internal alerts with external threat intelligence. They can quickly determine if a detected IP address is malicious, if compromised credentials are involved, or if the attack is part of a larger campaign, accelerating containment and remediation efforts.
Executive & Board-Level Risk Reporting
CISOs and IT leaders utilize Threat Watch's clear dashboards and risk scoring to communicate cybersecurity posture in business terms to executives and the board. The platform provides tangible metrics and trends that demonstrate risk reduction over time, justify security investments, and build organizational trust in the security program's effectiveness.
Third-Party & Supply Chain Risk Assessment
Organizations extend their security vigilance to their partners and vendors. By monitoring the digital footprint and breach exposure of key third parties with Threat Watch, companies can assess the risk posed by their supply chain. This enables informed decisions during vendor onboarding and creates leverage for requiring higher security standards from partners.
Overview
About Promotron
Promotron is a groundbreaking cloud-based platform revolutionizing the promotional products industry. Designed specifically for distributors, importers, manufacturers, and printing houses, Promotron integrates a comprehensive suite of software solutions to automate and digitalize the entire B2B workflow. From generating initial quotes to managing final deliveries, this platform enables businesses to escape the limitations of manual processes, unlocking new levels of efficiency and growth. With a core mission to simplify complexity, Promotron saves invaluable time through massive automation, allowing users to focus on what matters most—driving their business forward. By seamlessly blending e-commerce capabilities, advanced Web2Print technology, automated quoting, and robust supplier networks, Promotron offers more than just tools; it provides a complete digital ecosystem designed to enhance collaboration, streamline product and print data management, and deliver a superior shopping experience to end customers. With Promotron, businesses are not just adopting software; they are embracing a powerful engine for digital transformation and market leadership.
About Threat Watch
Threat Watch is your definitive command center for cybersecurity confidence, designed to transform fear and uncertainty into clarity and control. In a digital landscape where threats evolve by the second, operating with fragmented or delayed information is no longer an option—it's a critical liability. This powerful, unified intelligence platform is engineered to shatter the complexity of cyber risk, providing a real-time, holistic view of your organization's entire digital footprint. It continuously scans and analyzes everything from your internal network assets and software vulnerabilities to external exposures like compromised employee credentials, phishing domains, and dark web mentions. By synthesizing this intelligence into a single, actionable dashboard, Threat Watch delivers an immediate and precise picture of your cyber health. This empowers IT leaders, security teams, and business executives to move decisively from a reactive, fire-fighting posture to a proactive, strategic stance. The core promise is speed and precision: automate critical assessments, receive prioritized insights, and mitigate risks faster than ever. With Threat Watch, cybersecurity stops being a constant, draining challenge and becomes a measurable, manageable strategic advantage. It's time to stop just defending your perimeter and start leading your organization with certainty.
Frequently Asked Questions
Promotron FAQ
What industries can benefit from using Promotron?
Promotron is designed specifically for the promotional products industry, benefiting distributors, importers, manufacturers, and printing houses by streamlining their processes and enhancing efficiency.
How does Promotron improve the quoting process?
Promotron automates the quoting process, allowing users to generate detailed quotes, including pricing and virtual samples, in under 60 seconds. This significantly speeds up response times and enhances customer satisfaction.
What is the Web2Print technology in Promotron?
The Web2Print technology enables users to create print-ready data and conduct proofreading within a minute, reducing preparation time for promotional items and ensuring that products are ready for printing quickly and accurately.
Can Promotron help with e-commerce?
Absolutely! Promotron provides first-class e-commerce solutions, including a modern webshop for selling promotional goods and textiles, allowing businesses to offer custom products easily and enhance their online sales capabilities.
Threat Watch FAQ
How does Threat Watch discover my company's digital assets?
Threat Watch employs a combination of safe, passive reconnaissance techniques and authorized active scanning. It uses proprietary algorithms to discover domains, subdomains, IP addresses, and network ranges associated with your organization. For internal assets, a lightweight agent or secure API integration can be used with your existing systems to provide a complete, unified inventory without disrupting operations.
What makes Threat Watch different from a traditional vulnerability scanner?
While traditional scanners focus primarily on finding technical flaws in known assets, Threat Watch provides a holistic risk intelligence platform. It combines asset discovery and vulnerability assessment with external threat monitoring (dark web, breached credentials), business context, and intelligent prioritization. This gives you not just a list of bugs, but a strategic understanding of which risks pose the most immediate danger to your business.
Is the platform suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is designed for clarity and actionability. Its automated scanning, intuitive risk scoring, and prioritized recommendations are invaluable for IT generalists or business owners who need to manage security effectively without deep expertise. The platform guides you to the most critical issues, making efficient use of limited time and resources to achieve maximum risk reduction.
How quickly will I see results after starting with Threat Watch?
You gain value from the moment you initiate your first scan. The platform begins analyzing your provided domains and data immediately, with initial results and identified exposures often available within hours. Your comprehensive cyber health score and ongoing monitoring alerts begin from day one, providing immediate visibility and a baseline from which to measure your security improvement journey.
Alternatives
Promotron Alternatives
Promotron is a cutting-edge cloud-based platform designed to revolutionize the promotional products industry. With its comprehensive suite of automated sales and collaboration tools, it empowers businesses by streamlining the entire B2B workflow, enhancing efficiency and growth. Users often seek alternatives to Promotron for various reasons, including pricing concerns, specific feature sets, or unique platform needs that may better align with their business models. When choosing an alternative, it’s essential to consider factors such as ease of use, integration capabilities, customer support, and how well the platform can adapt to your specific operational goals. As you explore alternatives, focus on solutions that not only automate processes but also provide a user-friendly experience that fosters collaboration and innovation. Look for platforms that offer robust e-commerce functionality, advanced customization options, and the ability to manage product and print data seamlessly. By prioritizing these features, you can ensure that your chosen solution drives your business toward success and positions you as a leader in the ever-evolving promotional products landscape.
Threat Watch Alternatives
Threat Watch is a powerful business intelligence platform designed to transform cybersecurity management. It provides a unified command center for real-time digital risk assessment, moving organizations from a reactive to a proactive security posture. Users often explore alternatives to find the perfect fit for their specific needs, budget, and existing technology stack. The search for a different solution is common and driven by various factors. Some teams require deeper integration with niche tools, while others prioritize different pricing models or specific feature sets not covered by a single platform. It's a natural step in finding the right strategic partner for your unique journey. When evaluating alternatives, focus on capabilities that empower your team. Look for comprehensive visibility, actionable intelligence, and a platform that turns complex data into clear leadership insights. The goal is to find a solution that not only identifies threats but also accelerates your ability to act, transforming cybersecurity from an operational burden into a demonstrable business advantage.
