Threat Watch
Take command of your digital safety with an instant, comprehensive cybersecurity health scan.
AI tool Details
Explore More
Alternatives
About Threat Watch
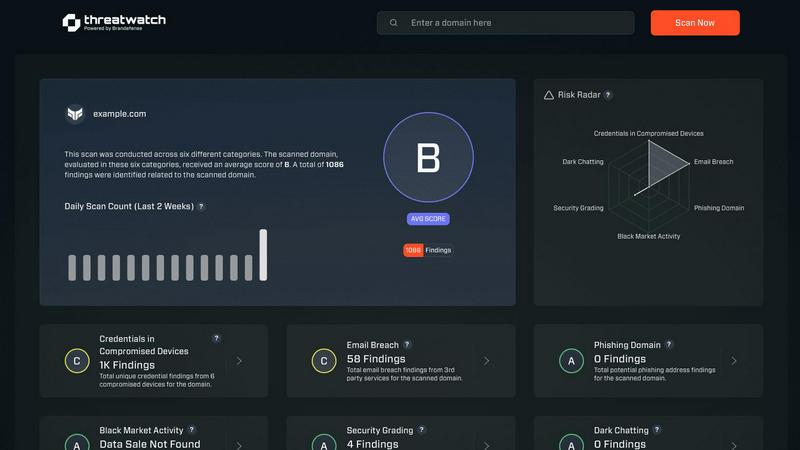
Threat Watch is your definitive command center for cybersecurity confidence, designed to transform fear and uncertainty into clarity and control. In a digital landscape where threats evolve by the second, operating with fragmented or delayed information is no longer an option—it's a critical liability. This powerful, unified intelligence platform is engineered to shatter the complexity of cyber risk, providing a real-time, holistic view of your organization's entire digital footprint. It continuously scans and analyzes everything from your internal network assets and software vulnerabilities to external exposures like compromised employee credentials, phishing domains, and dark web mentions. By synthesizing this intelligence into a single, actionable dashboard, Threat Watch delivers an immediate and precise picture of your cyber health. This empowers IT leaders, security teams, and business executives to move decisively from a reactive, fire-fighting posture to a proactive, strategic stance. The core promise is speed and precision: automate critical assessments, receive prioritized insights, and mitigate risks faster than ever. With Threat Watch, cybersecurity stops being a constant, draining challenge and becomes a measurable, manageable strategic advantage. It's time to stop just defending your perimeter and start leading your organization with certainty.
Features
Comprehensive Digital Footprint Analysis
Threat Watch goes beyond surface-level scanning to deliver a deep, continuous analysis of your entire digital presence. It automatically discovers and inventories all internal and external assets, including cloud instances, domains, and network devices, while simultaneously hunting for associated vulnerabilities. This 360-degree visibility ensures no blind spot is left unmonitored, giving you the complete picture needed for true security confidence.
Dark Web & Breach Intelligence Monitoring
Proactively defend against threats that originate in the shadows. Threat Watch constantly monitors dark web forums, paste sites, and private channels for mentions of your company's data, such as stolen credentials, intellectual property, or confidential plans. This early-warning system alerts you to breaches involving your employees or systems long before they can be weaponized, allowing for preemptive action.
Real-Time Compromised Credential Alerts
One of the most common attack vectors is through reused or leaked passwords. Threat Watch integrates with vast databases of known breaches to instantly alert you if employee email addresses and credentials appear in compromised data sets. This allows your security team to enforce immediate password resets and multi-factor authentication, shutting down account takeover attempts before they begin.
Actionable Risk Prioritization Dashboard
Information overload is paralyzing. Threat Watch cuts through the noise by synthesizing millions of data points into a clear, prioritized risk score and actionable insights. The intuitive dashboard categorizes risks by severity and potential business impact, telling you exactly what to fix first. This transforms raw data into a strategic roadmap, enabling efficient resource allocation and faster risk reduction.
Use Cases
Proactive External Attack Surface Management
Security teams use Threat Watch to continuously discover and assess all internet-facing assets owned by their organization. By identifying unknown or forgotten servers, misconfigured cloud storage, and vulnerable web applications, they can eliminate easy entry points for attackers before a breach occurs, dramatically hardening their external defenses.
Rapid Incident Response & Investigation
When a security alert fires, every second counts. Investigators leverage Threat Watch to instantly cross-reference internal alerts with external threat intelligence. They can quickly determine if a detected IP address is malicious, if compromised credentials are involved, or if the attack is part of a larger campaign, accelerating containment and remediation efforts.
Executive & Board-Level Risk Reporting
CISOs and IT leaders utilize Threat Watch's clear dashboards and risk scoring to communicate cybersecurity posture in business terms to executives and the board. The platform provides tangible metrics and trends that demonstrate risk reduction over time, justify security investments, and build organizational trust in the security program's effectiveness.
Third-Party & Supply Chain Risk Assessment
Organizations extend their security vigilance to their partners and vendors. By monitoring the digital footprint and breach exposure of key third parties with Threat Watch, companies can assess the risk posed by their supply chain. This enables informed decisions during vendor onboarding and creates leverage for requiring higher security standards from partners.
Frequently Asked Questions
How does Threat Watch discover my company's digital assets?
Threat Watch employs a combination of safe, passive reconnaissance techniques and authorized active scanning. It uses proprietary algorithms to discover domains, subdomains, IP addresses, and network ranges associated with your organization. For internal assets, a lightweight agent or secure API integration can be used with your existing systems to provide a complete, unified inventory without disrupting operations.
What makes Threat Watch different from a traditional vulnerability scanner?
While traditional scanners focus primarily on finding technical flaws in known assets, Threat Watch provides a holistic risk intelligence platform. It combines asset discovery and vulnerability assessment with external threat monitoring (dark web, breached credentials), business context, and intelligent prioritization. This gives you not just a list of bugs, but a strategic understanding of which risks pose the most immediate danger to your business.
Is the platform suitable for a small business without a dedicated security team?
Absolutely. Threat Watch is designed for clarity and actionability. Its automated scanning, intuitive risk scoring, and prioritized recommendations are invaluable for IT generalists or business owners who need to manage security effectively without deep expertise. The platform guides you to the most critical issues, making efficient use of limited time and resources to achieve maximum risk reduction.
How quickly will I see results after starting with Threat Watch?
You gain value from the moment you initiate your first scan. The platform begins analyzing your provided domains and data immediately, with initial results and identified exposures often available within hours. Your comprehensive cyber health score and ongoing monitoring alerts begin from day one, providing immediate visibility and a baseline from which to measure your security improvement journey.
Similar to Threat Watch
AI Business Name Generator
Unlock your brand's potential with our AI Business Name Generator, creating unique and catchy names for your startup or company in an instant.
FormRoyale
Run Smarter Surveys and Turn Feedback Into Actionable Insights
MarketWrk
Transform your pricing strategy with MarketWrk, automating retail price monitoring and MAP violation alerts for immediate action and insights.
Opal44
Transform your website data into clear, actionable insights with plain English AI analysis.
Fusedash
Transform raw data into clear dashboards so your team can instantly act on powerful insights.
finban
Transform your liquidity planning with finban for confident decisions on hiring, taxes, and investments—no more Excel.
Zignt
Zignt empowers teams to sign contracts instantly and securely, transforming how you work.
aVenture
aVenture empowers you to uncover venture intelligence and identify promising private companies for strategic investment.